

About the past two yrs, TikTok’s explosive progress has turn out to be a unusual illustration of a Chinese internet company’s good results in the West. In addition to TikTok, which we know perfectly in the intercontinental industry, a further identify for the app in the Chinese marketplace is Douyin. In fact, since TikTok has regularly reached the top rated obtain in its category, there have been sceptical observations about its use and safety of personal knowledge. As of January 2021, 43.7% of the buyers were being aged among 18-24 many years previous, and 31.9% for 25-34. Viewpoints are mostly divided on no matter whether to ban TikTok or refine the restrictions.

TikTok and Douyin

ByteDance and some of its subsidiaries
A couple times ago, Penetrum, an Web 2. organization, produced a complex investigation report on the TikTok app, which unveiled that in its source code, 37.70% of the identified IP addresses belong to Alibaba Group, a federal government-sanctioned ISP founded by Jack Ma, situated in Hangzhou, China. The group’s privateness plan states that they share and distribute the individual facts of their consumers.
It is true that, out of rational things to consider, we do not want to be prejudiced versus TikTok just because it is a subsidiary of a Chinese enterprise. Even so, it is really hard to consider corporations like ByteDance that have enormous influential power would be in a position to grow large without the assist of the Chinese federal government. Not only that, but quite a few reviews have demonstrated that even although TikTok has area procedure teams in the U.S. and Australia, employees at the parent corporation even now have obtain to information on abroad end users. Because of this unfettered authority, TikTok is in a quite different posture from Fb and Google, which also acquire large amounts of user details everyday.
TikTok Australia asserted that they are unbiased when confronted with uncertainties, giving the impact that they would not share user info with foreign governments. On the other hand, keep in intellect that it is a law in China for firms and citizens to share their details when expected by the appropriate authorities in name of ‘national stability.’
“When the app is in use, it has the means to scan the full difficult drive, entry the speak to lists, as properly as see all other apps that have been installed…..If you explain to Fb you don’t want to share something, it won’t ask you all over again. TikTok is significantly extra aggressive.” says Robert Potter, the co-CEO of World wide web 2..
According to a TikTok examination offered by Net 2., some obtain that TikTok requests do not appear to be to be necessary for a social media application:
- Reads the GPS location after for every hour (even when it’s jogging in the background)
- Scans all other applications operating on the phone
- Gathers the record of all applications set up on the cell phone
- Total obtain to study the clipboard
- Info of all accounts on the device
- Retreives a record of all data files on external storageByteDance
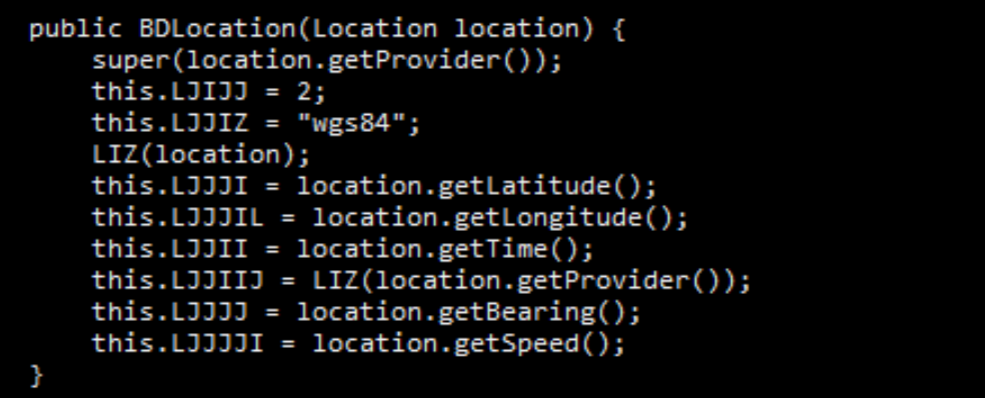
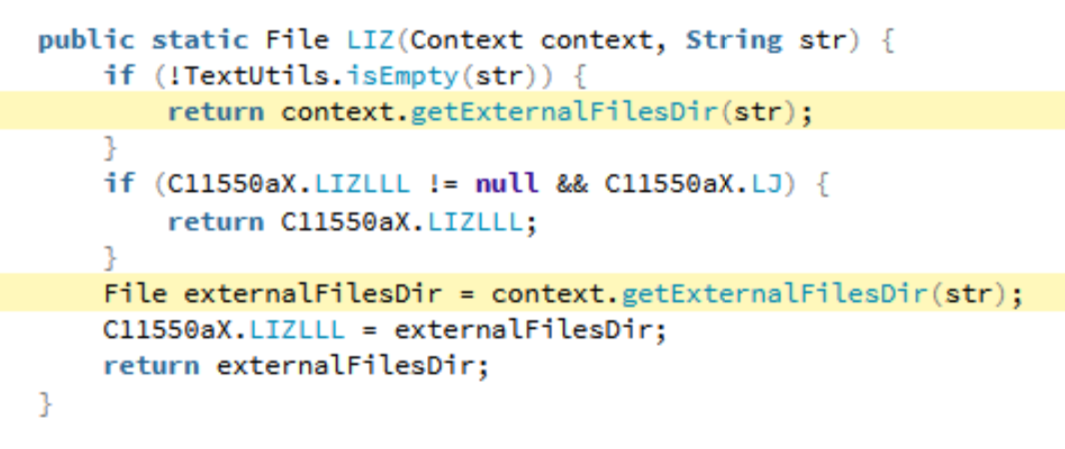
Get location code
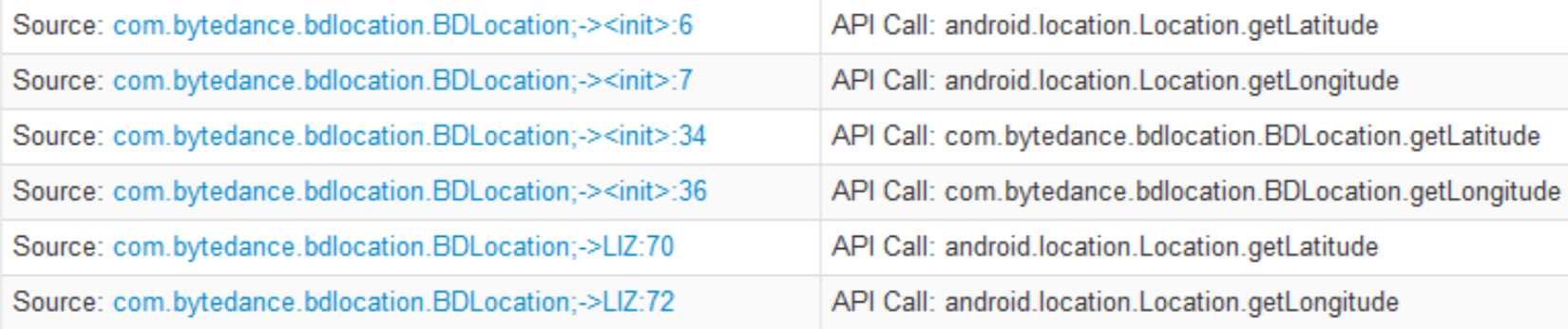
TikTok get longitude and latitude info requests

Get all purposes and running responsibilities on the unit
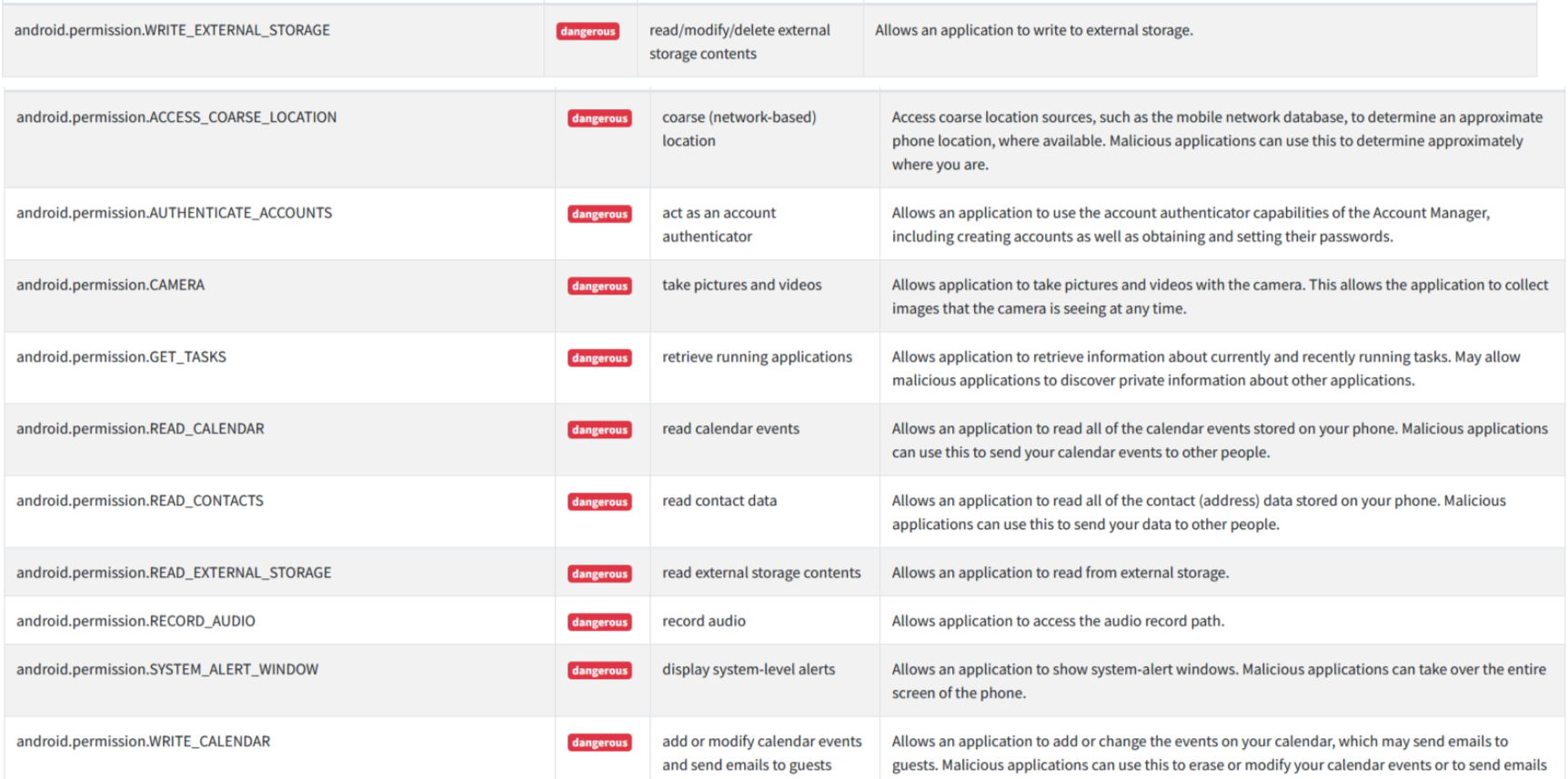
TikTok Android entry permissions
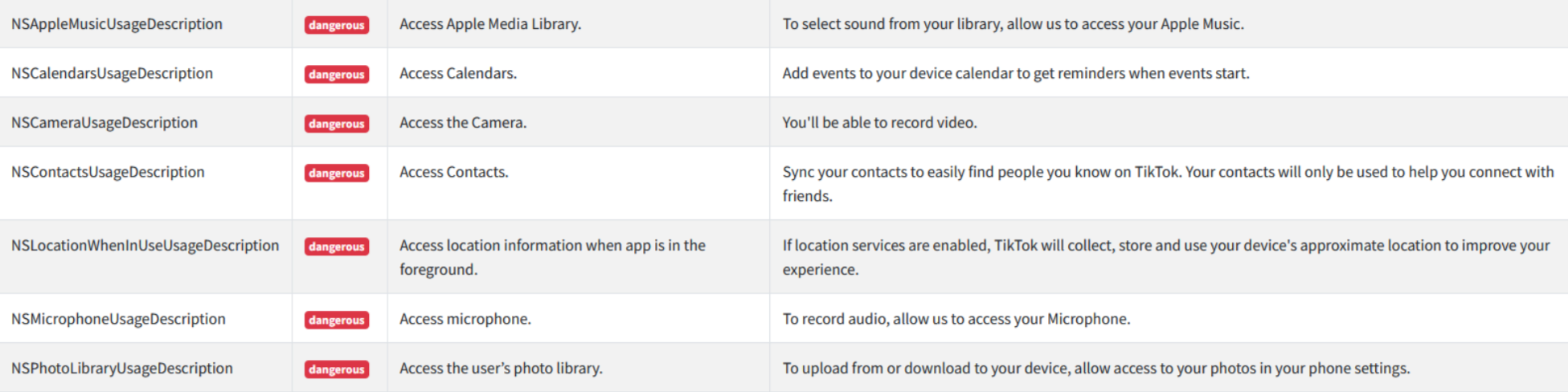
TikTok iOS access permissions
List anything in external storage
None of the permissions listed above must be essential. From the entry scale, it is additional of a harvesting behaviour that will perhaps guide to a a lot more useful end result for the company but hardly something to its finish people.
Whether or not it’s just a political soccer or authentic privateness threats, as stop customers, we do not always have to provide a optimistic reaction to the needs of requests for permissions from the application. Holding the permissions at a minimum amount degree would be excellent ample for the applications to do the task, for you.








